Cyber security – what to look out for in 2019

Acknowledging that criminal activity is becoming more sophisticated, in this article our experts highlight five areas of immediate concern and warn that businesses must be prepared or risk devastation. In recent years the cyber security challenge from hostile states and increasingly-well-organised criminals has contributed to a sense of uncertainty in society. Governments have not yet […]
Pandora’s Box
At the ITC Cyber Summit this year, which was well attended and according to feedback “interesting”, we made some predictions for the coming year. Amongst them was this: Containerisation, Cloud and Agile, what could possibly go wrong? There is a furious rush to migrate to cloud based containerised services and develop applications at breakneck speed […]
Cryo Currency
The news this week was alive with a story about the Canadian crypto-currency exchange QuadrigaCX , who’s CEO is unfortunately not (alive). Gerald Cotten, the aforementioned CEO is reported to have died in on the 9th December in Jaipur India, of complications from Crohn’s disease whilst apparently opening an orphanage. As well as being a shocking […]
REVERSE RDP ATTACKS

Priority: High Executive Summary: Researchers at Check Point have uncovered a number of vulnerabilities in three Remote Desktop Protocol (RDP) Clients: Microsoft’s RDP client, rdesktop, and FreeRDP, which can be exploited by a malicious server when the client connects to it over RDP. This would allow an attacker who had compromised a user’s device to […]
ZuckBook

Firstly, we would like to thank all of you who took time out of your busy days to attend our Cyber Summit yesterday in London. We heard from the venerable Paddy McGuinness CMG OBE (some say that it stands for Call Me God), who recommended that this is a year for self-reliance and being in […]
The Elastic band
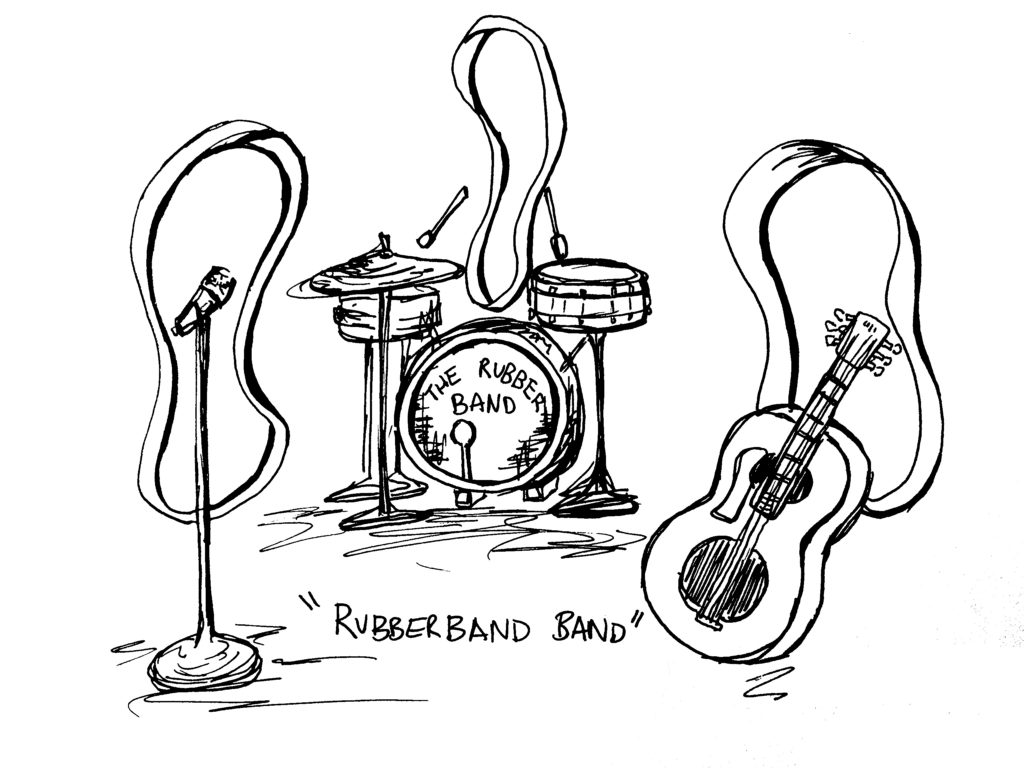
If you are a regular reader of this blog, you will be more than well aware that we have always been very concerned, if not paranoid about the impact of the misconfiguration of Internet facing services and applications. We have consistently advised that a massive problem with agile development and deployment cycles, alongside a pressure […]
Compla¢
As we have muttered and groaned (ad nauseum) about many times before, news of massive breaches with huge numbers of exposed details may well be giving us all breach fatigue. Even former presidents of the United States can be confused by these big numbers, allegedly (with apologies to our dear Brazilian friends): “Giving Bush his […]
January 2019

View our Cyber Bulletin for January here.
Better the devil you know

[vc_row][vc_column][vc_column_text css=”.vc_custom_1547551600712{margin-bottom: 0px !important;}”] In this article Glenn Fitton, ITC Senior Cyber Consultant, zooms in on ‘Threat Intelligence’, focusing on what it is, and what it isn’t. In the modern age of cyber and with the growing prevalence of large-scale cyber attacks, most of us have come to terms with the fact that it’s not […]
B B C
Not the (impartial) British public service broadcaster aka ‘Aunty’. We only have a page or so, which is nowhere near enough to summarise our thoughts on the corporation! We are talking about the implications of moving a business, via the digitalisation process, from a world in which online activity is predominately Business to Business, to […]
